THANK YOU FOR SUBSCRIBING

Penetration Testing Is an Important Driver in Automotive Cybersecurity
Yi (Estelle) Wang, Head of Product Cybersecurity and Privacy Office Singapore at Continental


Yi (Estelle) Wang, Head of Product Cybersecurity and Privacy Office Singapore at Continental
The coming generations of vehicles will be increasingly connected and software-enabled, paving the way for new functions in user experience, intelligent traffic management, autonomous driving, and more. However, connected mobility is also a target for hackers, and comprehensive cybersecurity testing is critical to identifying security loopholes in automotive products and services.
Penetration testing is one aspect that is growing in interest, as employing simulated cyberattacks can reveal potential vulnerabilities, especially at the later stages of product development. Additionally, penetration testing can also support vehicle manufacturers in complying with international standards and regulations.
1. Background of the latest international cybersecurity regulations and standards
On June 24, 2020, the World Vehicle Regulations Coordination Forum (WP.29) of the United Nations Economic Commission for Europe (UNECE) issued a regulation, Cybersecurity and Cybersecurity Management system (UNECE R155 in short). It aims to reduce the risk of cyberattacks and requires establishing a cybersecurity management system. In the European Union and other countries signed under the “UNECE 1958 agreement”, this regulation will be mandatory for all new vehicle types from July 2022 and will become mandatory for all new vehicles produced from July 2024.
Around a year later, the official version of ISO/SAE 21434, “Road Vehicles – Cybersecurity Engineering,” was announced on August 31, 2021 . This standard was developed by working groups of the International Organization for Standardization (ISO) and the International Society of Automotive Engineers (SAE).
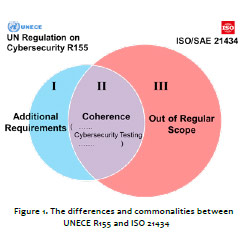
Differences and commonalities between UNECE R155 and ISO21434
In general, there are two differences between regulation and standards - ISO/SAE 21434 has a broader scope than UNECE R155, while the UN Regulation lays out additional requirements, especially in technical areas, as shown in Figure 1.
Where they both meet is in the requirements for cybersecurity testing and sufficient validation. According to several clauses under UNECE R155 (Clause: 5.1.1, 5.1.2, 5.1.3, 7.2.2.2, 7.3.6, 8.1.2, and 9.1.1), sufficient testing is compulsory to verify the effectiveness of the cybersecurity measures implemented throughout a product’s life cycle. In addition, vehicle manufacturers need to document the details of the Technical Services responsible for conducting approval tests.
Various sections in ISO/SAE 21434 (Chapters/sections: 10.4.2 [RQ-10-09], [RQ-10-10], 11.1 and 11.2) also spell out that testing shall be performed to confirm that unidentified weaknesses and vulnerabilities in the component are minimized through the verification and validation process.
Non-standard cybersecurity testing, or penetration testing, can play an important role.
2. Cybersecurity testing in automotive
Cybersecurity testing in the automotive industry is to address the following problems existing in the development phase, as shown in Figure 2.
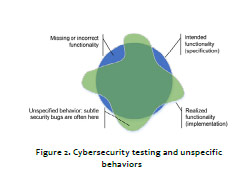
The summary of Figure 2. is as follows:
(1) Standard cybersecurity testing can verify most of missing or incorrect functionality in products due to gaps between intended functionality (in planned specification) and realized functionality (in practical implementation).
(2) The unspecified behavior of potential cybersecurity bugs and vulnerabilities is identified through non-standard cybersecurity testing or penetration testing (Under ISO 27001, penetration testing detects cybersecurity vulnerabilities and exhibits the practical probability of different attack scenarios)
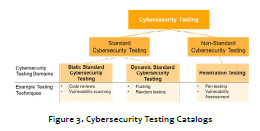
Standard cybersecurity testing aims to identify and reduce cybersecurity defects within a system during the design and development phases. It includes static and dynamic standard cybersecurity testing.
Non-standard cybersecurity testing aims to exploit cybersecurity defects by simulating real-world attacks from a hacker’s perspective after the development phase or in the late stage of the development phase. It includes penetration testing and vulnerability assessment.
3. Challenges in cybersecurity testing
Penetration testing (pen-testing) in the automotive industry presents unique challenges due to the trend towards the Software-Defined Vehicle (SDV), driven by advancements in connectivity, artificial intelligence, and software technologies. Key features of SDV include connectivity for real-time data exchange, over-the-air updates for remote software enhancements, integration of artificial intelligence for autonomous driving and advanced driver assistance systems, and a software-defined cockpit with customizable user experiences.
Penetration Testing Is One Aspect That Is Growing In Interest, As Employing Simulated Cyberattacks Can Reveal Potential Vulnerabilities, Especially At The Later Stages Of Product Development
The summary of challenges is as follows:
1. Complexity of Ecosystem: Modern vehicles can have hundreds of Electronic Control Units (ECUs) and multiple communication systems, making them very complex. Performing pen-testing for such a system requires specialized knowledge.
2. Real-Time Systems: Automotive systems often operate in real-time, requiring pen-testers to be aware of timing and resource constraints.
3. Supply Chain Cybersecurity: The automotive industry relies on a vast supply chain for components and software. Performing comprehensive pen-testing has to involve components throughout the entire supply chain.
4. Regulatory Compliance: Pen-testing must fulfill the technical recommendations from ISO/SAE 21434 and regulation requirements from UNECE R155.
5. Interoperability Challenges: Testing the security of interfaces between different components and systems within a vehicle or across vehicles can be challenging due to varying standards and protocols. This requires well-trained pen testers in the limited talent pool of cybersecurity.
Collaboration between automotive manufacturers, cybersecurity researchers, and regulatory bodies is essential to address these challenges effectively.
Continental offers end-to-end cyber security solutions from Argus and Elektrobit for all connected vehicle electronics. Both firms are subsidiaries wholly owned by Continental. Through this, we enable vehicle manufacturers to prevent, understand, and respond to cyber threats. Part of this process includes providing professional security services through Argus, which can offer pen-testing to support OEMs in fulfilling the requirements of the UNECE R155 regulations.
Weekly Brief
I agree We use cookies on this website to enhance your user experience. By clicking any link on this page you are giving your consent for us to set cookies. More info
Read Also
Driving It Transformation at Lactalis Australia
AI Adoption in Hospitality: Striking the Balance Between Innovation, Excellence and Trust
The AI Rat Race - Keeping Up with New Technologies or Waiting for Maturity?
The Role Of Digitalization In Transforming Airport Customer Experiences
From Chemical Solutions to Data Center Innovations
Ethics & Compliance in a Digital World: Navigating HCP Engagement in APAC
How AI is Driving Innovation and Customer-Centricity in Insurance
The Impact of Smart Infrastructure on Growing Cities





















