Read Also
Empowering Educators with Faith, Excellence and Purpose
Amelia Febriani, Head of Training and Development, Mawar Sharon Christian School Official
Leading with AI: From Ethics to Enterprise Impact
Adrienne Heinrich, AI COE Head, Senior Vice President, Union Bank of the Philippines
Done Today Beats Perfect Tomorrow: The New IT Advantage
Samuel Budianto, Head of Information Technology,Time International
The Shift from Cybersecurity to Product Security: A Business Imperative
Peter Wong, Head of Information Security and Compliance, Apac, Edenred
Advancing Retail through E-Commerce, Cloud and Cybersecurity
John Gaspar Antonio, CIO/Vice President for Information Technology & E-Commerce / Data Protection Officer, Metro Retail Stores Group
Transforming Risk Management into Strategic Business Advantage
Jeremy Leong, Chief Risk Officer and Head of Risk and Compliance, Taishin International Bank – Brisbane Branch
Designing Future-Ready, People-Centered Workplaces
Peter Andrew, Executive Director, Head of Workplace Strategy, Advisory Services, Asia Pacific, CBRE
Shaping Customer Experience Through Smarter Logistics
Pascal Kouknas, General Manager of Logistics, Shipping, and Information Technology, Freedom Australia













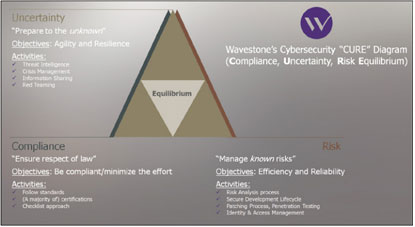 Most organizations have put a risk management framework in place. They identify their risks, assess and prioritize them, get a risk appetite stance from senior management and mitigate them. The more advanced companies have several lines of defense, which may include a first line that enforces the mitigation measures, a second line that controls them, and a third line (usually internal audit or an external authority) to measure actual efficiency.
This risk-based approach has allowed organizations to make a leap forward in terms of risk understanding and preparation. Unfortunately, in Asia, a passive push-back still exists against it. The notion of, “If nothing bad happened in the past, nothing bad will happen in the future,” is still a widespread mindset. It is even worse than the eternal “demonstrate security ROI”, because it fails to even acknowledge the existence of a threat.
However, Risk Management prepares you for the known risk, that is to say—to use insurers’ vocabulary—a risk for which distribution is known. You can estimate a likelihood and an impact. For instance, we know today that skipping the penetration testing phase in an IT project will inevitably lead your system to hold vulnerabilities, and we foresee pretty accurately which ones.
Risk, of course, needs to be addressed, but it will not be enough anymore. For the last decade, the cybersecurity industry has embraced the idea that incidents will eventually happen: you will not be able to simply prevent them, you have to be ready to detect them, and respond.
You Now Need to Manage Uncertainty
Cybersecurity has always been inspired by the armed forces. The principles of “DMZ”, “defense in depth”, and “kill chain” were not invented by computer scientists!
It is now time for the cybersecurity community to fully embrace another military concept: uncertainty management. This is the concept of handling risk that is not well understood, and for which the distribution is not known.
The difference between risk management and uncertainty management is comparable to peace time versus war time. In the former, you manage your level of crime, you know which actions will lead to which effects, and you can keep accurate statistics about the crime rate. In the latter, which in the cyber space would take the form of a major attack, the course of action is different: you want to avoid chaos and destruction, and face any possible “strategic surprise”.
Over the last decade, the more advanced companies in terms of cybersecurity have launched a number of initiatives that can all be considered as part of a new wave of “uncertainty management”. These strategies include threat intelligence and information sharing, red teaming, and the now popular cyber-crisis drills. While gaining momentum, far too many organizations still confuse risk and uncertainty management. Risk management requires clear rules, proper procedures, and managers to enforce them; while uncertainty management requires providing more autonomy to teams encouraging the use of common sense, and growing strong leadership.
Cyber Peace, Cyber War
A number of companies in Asia are solely focusing on doing the bare minimum that is required by law. To these, we say: wake up, you are probably already under attack and refuse to see it. Risk management is not an option anymore, and it is not done by “being compliant”. The latter will clear regulatory duties (and maybe your conscience) but not keep you safe.
Organizations have started preparing for uncertainty management with diverse levels of maturity and means, as the field is still relatively new.
In these times, one of the many roles of a Chief Information Security Officers will become to tell their Senior Management if the organization is at peace or at war, and how to prepare for the latter.
For this, the armed forces teach us one last lesson: the two types of scenarios to focus on are 1/ the most likely and 2/ the worst. Prepare for these, and you might be ready for everything in between.
Most organizations have put a risk management framework in place. They identify their risks, assess and prioritize them, get a risk appetite stance from senior management and mitigate them. The more advanced companies have several lines of defense, which may include a first line that enforces the mitigation measures, a second line that controls them, and a third line (usually internal audit or an external authority) to measure actual efficiency.
This risk-based approach has allowed organizations to make a leap forward in terms of risk understanding and preparation. Unfortunately, in Asia, a passive push-back still exists against it. The notion of, “If nothing bad happened in the past, nothing bad will happen in the future,” is still a widespread mindset. It is even worse than the eternal “demonstrate security ROI”, because it fails to even acknowledge the existence of a threat.
However, Risk Management prepares you for the known risk, that is to say—to use insurers’ vocabulary—a risk for which distribution is known. You can estimate a likelihood and an impact. For instance, we know today that skipping the penetration testing phase in an IT project will inevitably lead your system to hold vulnerabilities, and we foresee pretty accurately which ones.
Risk, of course, needs to be addressed, but it will not be enough anymore. For the last decade, the cybersecurity industry has embraced the idea that incidents will eventually happen: you will not be able to simply prevent them, you have to be ready to detect them, and respond.
You Now Need to Manage Uncertainty
Cybersecurity has always been inspired by the armed forces. The principles of “DMZ”, “defense in depth”, and “kill chain” were not invented by computer scientists!
It is now time for the cybersecurity community to fully embrace another military concept: uncertainty management. This is the concept of handling risk that is not well understood, and for which the distribution is not known.
The difference between risk management and uncertainty management is comparable to peace time versus war time. In the former, you manage your level of crime, you know which actions will lead to which effects, and you can keep accurate statistics about the crime rate. In the latter, which in the cyber space would take the form of a major attack, the course of action is different: you want to avoid chaos and destruction, and face any possible “strategic surprise”.
Over the last decade, the more advanced companies in terms of cybersecurity have launched a number of initiatives that can all be considered as part of a new wave of “uncertainty management”. These strategies include threat intelligence and information sharing, red teaming, and the now popular cyber-crisis drills. While gaining momentum, far too many organizations still confuse risk and uncertainty management. Risk management requires clear rules, proper procedures, and managers to enforce them; while uncertainty management requires providing more autonomy to teams encouraging the use of common sense, and growing strong leadership.
Cyber Peace, Cyber War
A number of companies in Asia are solely focusing on doing the bare minimum that is required by law. To these, we say: wake up, you are probably already under attack and refuse to see it. Risk management is not an option anymore, and it is not done by “being compliant”. The latter will clear regulatory duties (and maybe your conscience) but not keep you safe.
Organizations have started preparing for uncertainty management with diverse levels of maturity and means, as the field is still relatively new.
In these times, one of the many roles of a Chief Information Security Officers will become to tell their Senior Management if the organization is at peace or at war, and how to prepare for the latter.
For this, the armed forces teach us one last lesson: the two types of scenarios to focus on are 1/ the most likely and 2/ the worst. Prepare for these, and you might be ready for everything in between.









